General Discussion
A place to talk about whatever you want
180
Topics
1.7k
Posts
Morning lovely people. Having just had some new rads put in, I dumped the old TRVs for snacky enw Zigbee ones, which work great.
Currently my gas boiler has a Horstman Z-wave relay bound to a remote thermostat so only comes on depending on when the thermostat puts out a call for heat
Has anyone else got all their rads on TRVs and if so, how are you managing boiler control?
I'm thinking about using a Reaction that effectively says 'If any TRV is 'on', turn the boiler on by raising the setpoint on the thermostat' and vice versa.
Currently this isn't great as we have two rads (one in the kitchen (which has underfloor heating) and in the hall, (where the remote thermostat is) which don't have TRVs. If I set the thermostat to 25 (say) when a rad calls for heat, those two rooms get roasting no matter what else is going on.
So my thoughts are:
Add TRVs to these two rads and all will be well.
Is this a sensible approach, or is there a better way of doing it? Thanks, as ever!
C
Another question to the hive mind. Prompted by the fact that I lost yet another z-wave device over the weekend due to a power issue. It looks like z-way server is reporting another device failed (although it's working fine) and message queue is far too long IMHO. Also the failed device has been removed in the expert interface, but still there in the 'normal' one. Sigh.
Currently I have z-wave, Tuya, thinking about Zigbee.... Does anyone use one single protocol for everything? Right now I'm feeling that as the z-wave stuff dies, I'm just gonna replace it with something else....
C
Not really Smart Home stuff, but going to ask as we have smart people...
Bear with me on this one. Asking here because of the font of knowledge!
For many eek years I have had a Virgin V6 box and a Raspberry Pi running Kodi connected to my TV through a cheap *** HDMI switch. It all worked beautifully but the absolutely critical thing was that the TV remote passed the signals back to the Pi to allow remote control of Kodi.
Couple of changes of late:
Installed a soundbar on the TV using the ARC (audio return channel). That then turns the soundbar on and off when the TV turns on and off and the TV volume control controls the soundbar volume direct.
Everything continues to work
Upgraded the software of the Tivo box to Virgin 360. This is literally software only. You get sent a snacky new Bluetooth remote hit 'upgrade' on the screen and off it goes.
Now, things are not playing well. Typically when I turn on to watch Kodi the soundbar comes on (as it should) but the TV either puts out sound through its own speakers and the soundbar, or just the soundbar. It's not possible to control the volume of the soundbar through the TV. Also it's not longer possible to control Kodi using the TV remote.
If I turn the TV360 box off, i.e. power it down, before turning on to watch Kodi, everything is fine.
This makes little to no sense to me. My assumption is that the cheap *** HDMI switch is getting something from the TV360 connection that it didn't used to get when the software was Tivo and that's screwing up the HDMI communications. I'm upgrading the switch to something a little less chap, but wondered if anyone could validate my theory at all?
TIA
C
...is back....
https://arstechnica.com/google/2025/08/researchers-use-calendar-events-to-hack-gemini-control-smart-home-gadgets/?utm_source=facebook&utm_medium=social&utm_campaign=dhfacebook&utm_content=null&fbclid=IwY2xjawMBq-pleHRuA2FlbQIxMQABHlSqIalzbz1IxcJFzlw8GBE6nC3FwvxcHgR370nJhogU6JjqbmRxG-lysqgh_aem_lx9XboYFKw9tpHnedGQKUA
C
Following on from my last thread, some progress has been made over the weekend.
With 18G of spanky RAM in my Synology DS224+. I've jumped into the murky world of virtualisation and already eliminated the need for two Raspberry Pi's from my system.
Home Assistant: In theory they provide an OVA file which is supported by the Synology. I couldn't get it to work, however, so grabbed a copy of the .img file they supply, renamed it .iso and imported it as a VM. Restored from my full back up and that all seems fantastic.
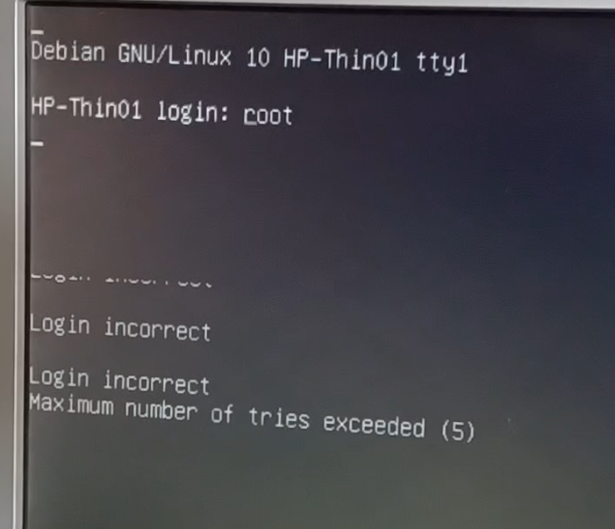
Minidnla Music server: Trivial. Grabbed a Debian .iso for Bookworm and copied that onto the NAS. Created a new machine which mirrored the specs of the Raspberry Pi, booted from the ISO then did an expert install. Once that was all stable with a basic core of stuff and networking, I've made a copy of that as a good base system. Then fired up minidnla on it, mounted my media and that's also woking. Not bad for a short weekend's work.
Still not sure about the main NUC though. I'm thinking of buying a new USB stick so I can mess around getting it working on the Synology before I do anything drastic.
Once that hurdle is sorted I'm torn between:
Using a brand new install of Bookworm, re-installing Z-way server, OpenLuup, AltUI, MSR and HA bridge, then restoring across or
Making an ISO of the current system, importing that and upgrading in place (which will be pretty risk free since I can snapshot everything before I make any changes.)
Decisions, decisions.
C
Hi everyone. Thanks for all your input recently on the topic of local notifications. I think we got some really interesting solutions
Back to more prosaic matters. Most of you will know that I've been messing around with this stuff for some years. My last major change was when I migrated from Vera, which was something like 4-5 years ago.
While my system has grown, it's not really altered very regularly, although I try to keep most of it kind of up to date.
Current set up:
Intel NUC that runs:
Bare metal install of Debian
Z-way server with Z-wave.me USB stick
Openluup
Altui
Multi system reactor
HA Bridge
Mosquito
Raspberry Pi
Running Home Assistant
About 40 varied Z-wave and Wifi devices
I also have a Synology DS224+ which may inform some responses.
Home Assistant recovery is pretty simple. I get a full backup of the system every night dumped onto my SAN and I know from experience that it would simply be a case of booting up a new install and feeding it the backup.
The NUC on the other hand....
Coming from a commercial IT world, I am becoming more and more conscious that I don't really feel I have a suitable disaster recovery plan, and my core system is running on hardware heading for 10 years old.
My initial thought, which I've kept putting off as it's awkward would be to grab a nice SSD, reboot the NUC into Mint or something similar and simply do a dd copy onto a new drive. I can get a replacement NUC on ebay simply enough, and keep it in a cupboard if anything other than the hard drive fails on the existing one, but this feels rather like a stop gap. However one immediate question:
If I had to use the replacement NUC would all the Z-wave devices simply carry on talking to the stick, or would they all need to be re-paired?
How easy would it be to move everything the NUC does (as a start) onto the NAS? Create a VM and clone the disc onto it?
Should I move to Docker? Something else?
What are the hive mind's thoughts?
Apologies if we've done this before, but while it all just works...
Cheers!
C
Just bought a couple of generic smart plugs and set them up easily using SmartLife app in the house I then plugged one into a workshop over 100m away This workshop has a hardwired internet connection with a separate wireless access router (not mesh) after doing a reset on the device and pairing to the new router it actually works from the house when my phone is connected to a completely separate wifi network - how is that possible ?
I did read something about these devices connecting to a server somewhere in China similar to IP cameras but there is no lag
I need to replace about 15 traditional wall light switches (no neutral wire) to turn on/off all lights with one operation inside the warehouse. And still maintain the ability to control each light individually.
The preference is not to set up a Wifi for each switch to reduce the number of devices connected to the network, and also, they change the Wifi password regularly, so they do not want to change all 15 switches.
I am looking for some solution that will achieve this with either Bluetooth/RF or any other technology.
The warehouse dimensions are about 100ftx100ft with sheetrock walls.
Please assist.
I thought I had created a topic on this some time back, but can't find it to close the loop.
The issue was the lights on my drive appeared to be randomly switching on, with nothing from MSR logging and just a simple 'turn this on' in Openluup logs.
Finally got to the bottom of it this morning, which might help someone.
Turns out that somehow Alexa has decided that my drive lights are part of my Living room. If I tell her 'Living room lights on' the drive lights also come on. And if I tell her to turn them off, they also go off.
Which is madness because they are NOT in the living room group.
Current solution is to disable the drive lights in the Alexa app, which is fine as I never need to voice control them.
C
Hi All
Hopefully this place looks like a helpful forum as I’m quite new to all this!
I’ve had a few devices all working separately /through their proprietary apps but we’re just finishing off a large house extension and this has added to the list.
I’d ideally like to be able to view/switch a number of different devices on one screen/head end but have no idea where to start.
The devices we have/will have shortly are as follows;
Zigbee Smart Sockets
Zigbee smart switches (for lights)
Heatmiser Neo Underfloor Heating (this runs from a Samsung ASHP but that part is automatic)
Samsung VRF air conditioning (currently using Smart Things App)
Hive (2xLTHW heating circuits in the existing house and Hot Water)
Ring (doorbell!)
Hik Vision PoE CCTV
We have lots of appliances (Neff N70) which we can control remotely but not too fussed about controlling those at the
Moment)
Any help/recommendations would be appreciated!
Thanks
Adrian
I have a legacy home automation set-up running on Windows XP. the computer and software have now died.
I have written a very nice Excel VBA program to replace the software and it can run on any modern Windows system.
My only remaining problem is to output the correct signal to a USB port to trigger the wireless switches.
Has anybody done a similar exercise. Please help.
Hi All,
Kind of new to Home Automation. Started off Using Amazon Echo units and added a Samsung SmartThings hub. I have mostly been using plug in modules for turning lights on and off. I live in a very rural area where the internet goes out a lot. I eventually want to change to to a non internet Hub so things will work without needing an internet connection. But I will post with those questions at a later date.
So, the task at hand is this: I have flood lights at each corner of my house. They are currently controlled by switches at the front and back doors. I would like to add Security Cameras to each corner also. I can easily find small Wifi switches to put into the electrical box where the flood lights are located, then I can terminate the leads together behind the Decora switch to have constant power. Then I can use the constant power up at the lights electrical box to power the security cameras. I would also like to have a wireless switch to take the place of the Decora switch to be able to turn the lights off and on.
I cannot seem to find a product like this. It seems I can find the small wired in switch boxes that will also come with external smart wall switches, but the wall switches are an external box that does not fit in or cover the existing Wall switch electrical box. I can also find Wireless Decora switches that come with a remote wired in small switch box , but they all seem to be RF and do not integrate with a Smart Hub.
I am hoping someone here knows of a product that matches what I am looking for. Any help would be appreciated.
Also any recommendations for Wireless Security cameras are welcome.
Thanks for any help.
Dear Forum,
I am just starting a smart home system. I've wanted to do this for 10 years at most and really would like to get a start. What I have are a couple of SONOFF wifi relays, some 433 (Hz/mHz) switches ( not wifi ) a couple of wifi lightbulbs, and I'd like to expand wifi thermostat, leak/water detectors, garage door openers and what ever else I can think of.
In the SONOFF items I have it's a particular app, the wifi bulbs are another app, and if I do a thermostat there might be another app. My wife is not a Luddite but she damn sure doesn't want to have to trouble shoot if/why a particular app breaks down.
So in what I do understand about smart home things is that I need/want a HUB. I spent 15 years doing some programming so I do have some computer ability, though I'd prefer to stay away from HAVING to line command operate the hub.
I would like a list of HUB's that people have found to be the best. Even better are links to let's say Amazon for that hub.
Regards from Noob Smart Home,
Barry
Hello lovely people. Long time and all that. Hope you're all doing OK.
Bit of a left field one here, looking for extra eyes more than an answer and you're the most logical bunch I know
Part of our HA system is a Logitech Elite hub and remote control.
This is programmed to control my Cyrus Stereo, our TV, and HDMI switch and our Virgin V6 box.
I've been away for a couple of days. Got back this evening to (eventually) work out that the V6 box appears to be not accepting any commands from the Logitech.
Everything has been rebooted.
Logitech uses IR to control
Cyrus: Fine
TV: Fine
HDMI: Fine
Remote control uses Bluetooth to control Hub.
All commands from the Remote to the hub are executed (one might assume correctly) as the activity LED responds, and if you're controlling (say) the Cyrus, all works fine.
iOS App can be used to control Hub over the WLAN:
All commands from the App re executed (one might assume correctly) as the activity LED responds, and if you're controlling (say) the Cyrus, all works fine.
Native remote (that uses as far as I know bluetooth) to control the V6 box works fine.
V6 box refuses to acknowledge any command other than from the native remote. Remote or app provoke absolutely zero response from the V6 box.
This is annoying, but damned if I can think of any logical reason. One might assume a firmware update on the V6 box, but given that the Hub simply emulates the native remote, that seems unlikely.
I'm struggling to think of where even to start troubleshooting this, so any random thoughts would be appreciated.
My initial approach is to buy another hub in case there's a different radio set that's failed in the hub...
TIA!
C
I currently have an HVAC system in the attic - for heating and A/C. 120v is supplied to the unit to run the gas heating. A/C uses 240v. I have an ecobee thermostat...which sometimes goes offline....not often. When it goes offline, I need to turn the 120v power to the HVAC system off and then back on (the ecobee gets its power from the HVAC system). That resets the ecobee and all is fine. I spend the summer away from this house and if the ecobee goes offine..I have no current method to reset the HVAC 120v power remotely. My idea is to replace the current 120v plug in the attic with a smart plug...then I can remotely turn the 120v power off and the ecobee will reset and come back online. I use Wyze and Lutron Casita in the house currently and was hoping I could find an in-wall smart plug from Wyze or Lutron. Obviously, I don't need diming, etc...just the ability to turn the plug power on/off. I've seen some options...but one problem I have is the attic can reach up to 135F in the summer...many of the smart plugs I've seen are not rated for that temperature. Might any of you have any thoughts on a smart plug I might want to look at? I don't want to invest in anything that would require a new hub - so either WiFi based or Casita HUB based. I need 120v and 15amp ratings. Thanks in advance.
BACKGROUND
I have been using 4 x Yale Contactless Connected Door Locks for several years (they use either a rfid tag or code to enter)
I have also been using 1 x Yale L1 Door Lock on the main front door and this connects via Yale Software
Yale contacted me to advise the L1 Lock software was being withdrawn and I needed to install a Yale Access Module into the existing lock and a Wi-Fi Bridge to link it with the newly released software
ALL of the above was working just fine.
RECENT
Yale emailed to advise I should add a Yale Access Module to each of the 4 other locks as this would link with the updated software via the Wi-Fi Bridge.
They offered a deal of just £4 each for these Modules so I got them.
THE PROBLEM
I found that only 2 of these modules would slot easily into the locks - two of them bent the pins and one of those snapped the female part in a lock (I do have a spare lock but thats not the point).
Anyway, I began to set-up the two fitted Modules with the Wi-Fi Bridge and I eventually found (thanks Google, NOT Yale) that I now need 1 x Wi-Fi Bridge PER LOCK (£50 each).
QUESTION
Does anyone know of a compatible Wi-Fi Bridge which works with Yale AND can handle multiple connections (ie 5 all 5 of my locks) ?
THANK YOU
-
-
This topic is deleted!
Unsolved -
-
-
-
-
-
-
Building a New Z Wave Network
Unsolved -
-
-
-
This topic is deleted!
Unsolved -
RPI 4B 2GB Available in NL
Unsolved -
-
Smart door lock
Unsolved -
This topic is deleted!
Unsolved -
-
-